The Invisible Biometric
In the realm of cybersecurity and user experience (UX) research, the way a user interacts with their peripherals is as unique as a fingerprint. Mouse movements—velocity, acceleration, jitter, and click latency—contain rich behavioral signals that are often overlooked. Capturing this high-frequency data without impacting system performance or user privacy presents a unique engineering challenge, yet it unlocks powerful capabilities for continuous authentication and bot detection.
The Challenge: High-Fidelity Data Capture
Building a production-grade mouse logger requires balancing granularity with efficiency:
- Sampling Rate vs. Performance: To capture meaningful micro-movements, the system must sample at 60Hz or higher. Doing this in a browser (JavaScript) without blocking the main thread and causing "jank" is non-trivial.
- Data Volume: A single session can generate megabytes of coordinate data. Transmitting this raw stream to a server in real-time is bandwidth-prohibitive.
- Cross-Platform Consistency: Operating systems and browsers handle pointer events differently (e.g., raw input vs. smoothed coordinates), requiring a normalization layer.
The Solution: A Lightweight Telemetry Agent
TendersLab engineered the "Mouse Logger," a highly optimized client-side library designed for stealthy, low-overhead behavioral data collection.
1. Event Throttling & Compression
We implemented an adaptive sampling algorithm that captures high-fidelity data during active movement but intelligently throttles down during idle periods. The data is delta-encoded and compressed using a custom binary format (Protocol Buffers) before transmission, reducing payload size by over 80% compared to standard JSON.
2. Feature Extraction at the Edge
Instead of just sending raw (x, y) coordinates, the client-side agent pre-calculates derived features such as angular velocity, curvature, and pause duration. This "edge computing" approach reduces the load on the backend and allows for immediate local heuristics (e.g., detecting a robotic "jump" movement).
3. Behavioral Biometrics Engine
On the server side, a Recurrent Neural Network (RNN) processes the time-series data to build a "behavioral profile" for each user. The model learns the user's unique motor control patterns, allowing it to flag anomalies—such as a remote access trojan (RAT) or an unauthorized user—with high confidence.
Impact: Security & UX Insights
The Mouse Logger has proven to be a versatile tool for both security and product teams:
- 99% Bot Detection Rate: The system successfully distinguishes between human users and advanced scripts that attempt to mimic human mouse movement, securing high-value transaction flows.
- Continuous Authentication: For enterprise clients, the tool provides a passive second factor of authentication, locking the session if the user's motor behavior changes drastically (indicating a potential account takeover).
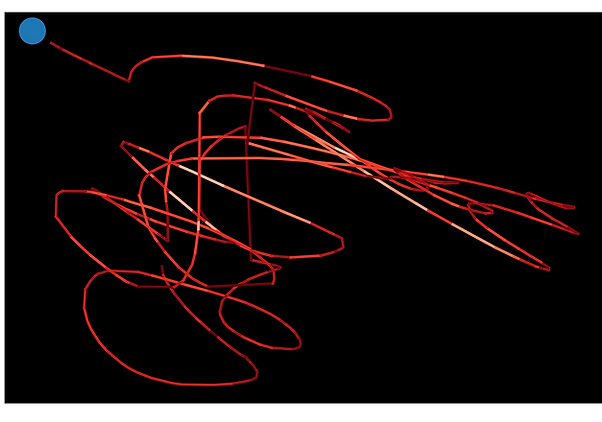
- Granular UX Heatmaps: Product designers use the aggregated data to visualize "rage clicks" and hesitation points, identifying UI friction areas that traditional analytics miss.